GitHub - x1sec/citrixmash_scanner: A fast multi threaded scanner for Citrix ADC (NetScaler) CVE-2019-19781 - Citrixmash / Shitrix

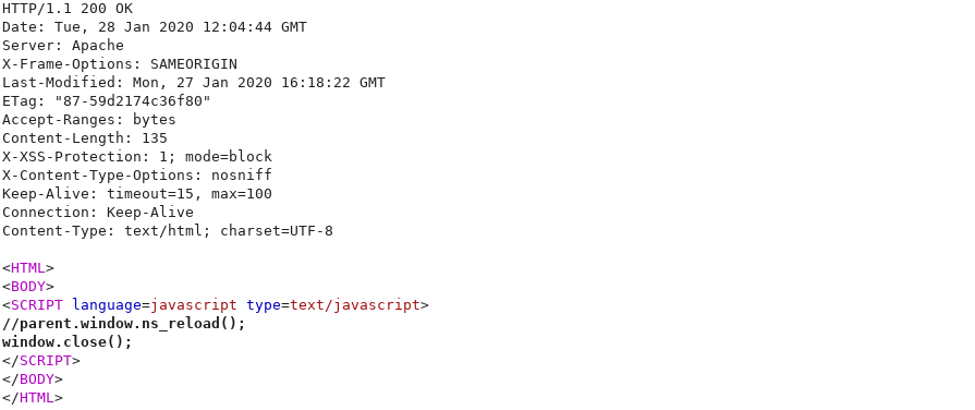
NMAS Click Jack Security Vulnerability: X-Frame-Options or the Content-Security-Policy's frame ancestor option missing to prevent Click Jacking attacks

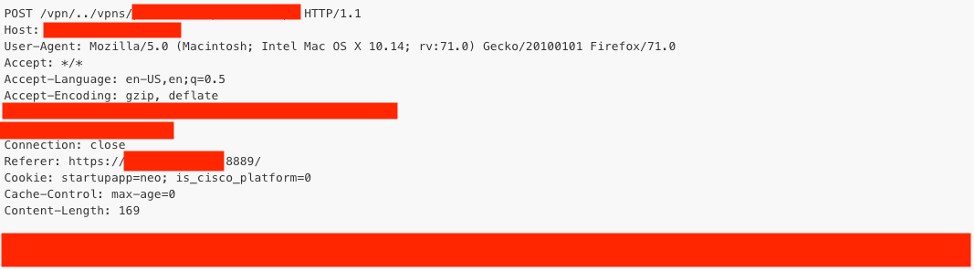
CVE-2019-19781: Critical Vulnerability in Citrix ADC and Gateway Sees Active Exploitation While Patches are Still Not Available - Blog | Tenable®

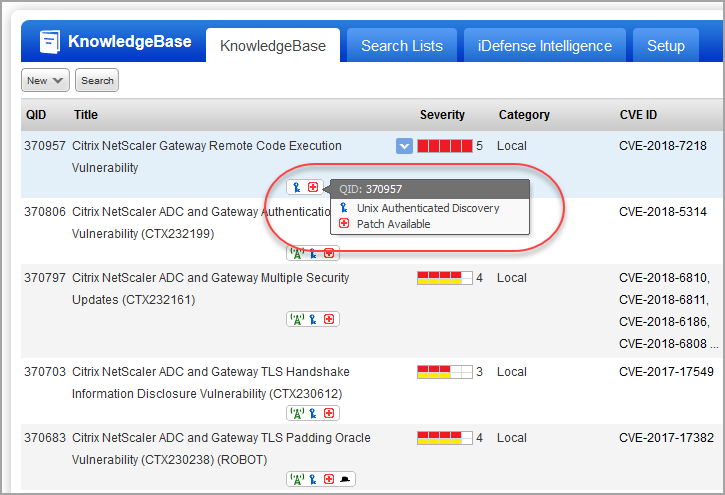
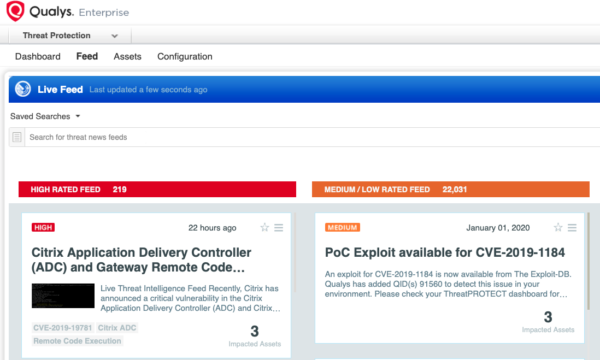
How to Configure NetScaler Application Firewall Signatures Protection Based on Vulnerability Scan Result of QualysGuard

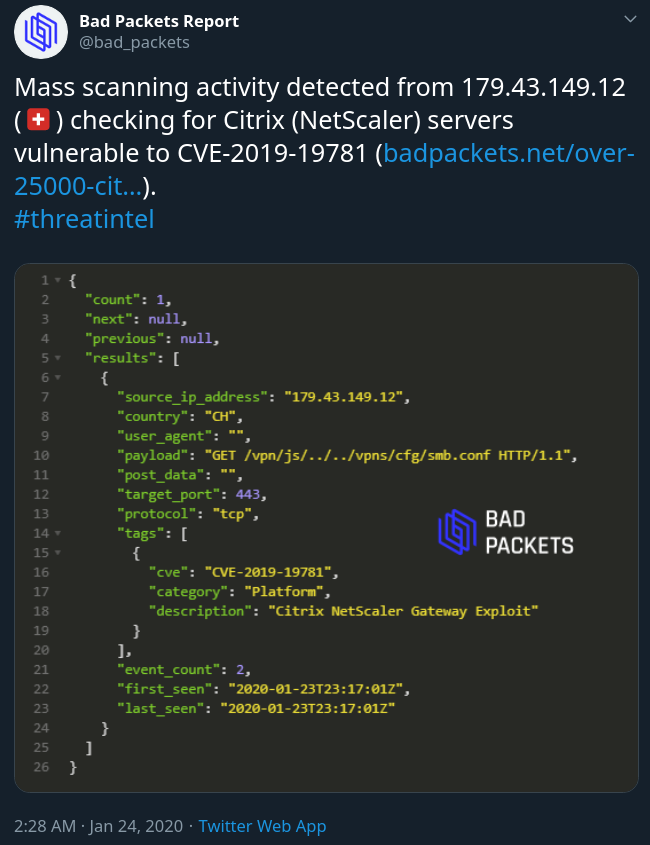
CVE-2019-19781: Critical Vulnerability in Citrix ADC and Gateway Sees Active Exploitation While Patches are Still Not Available - Blog | Tenable®

How to Configure NetScaler Application Firewall Signatures Protection Based on Vulnerability Scan Result of QualysGuard
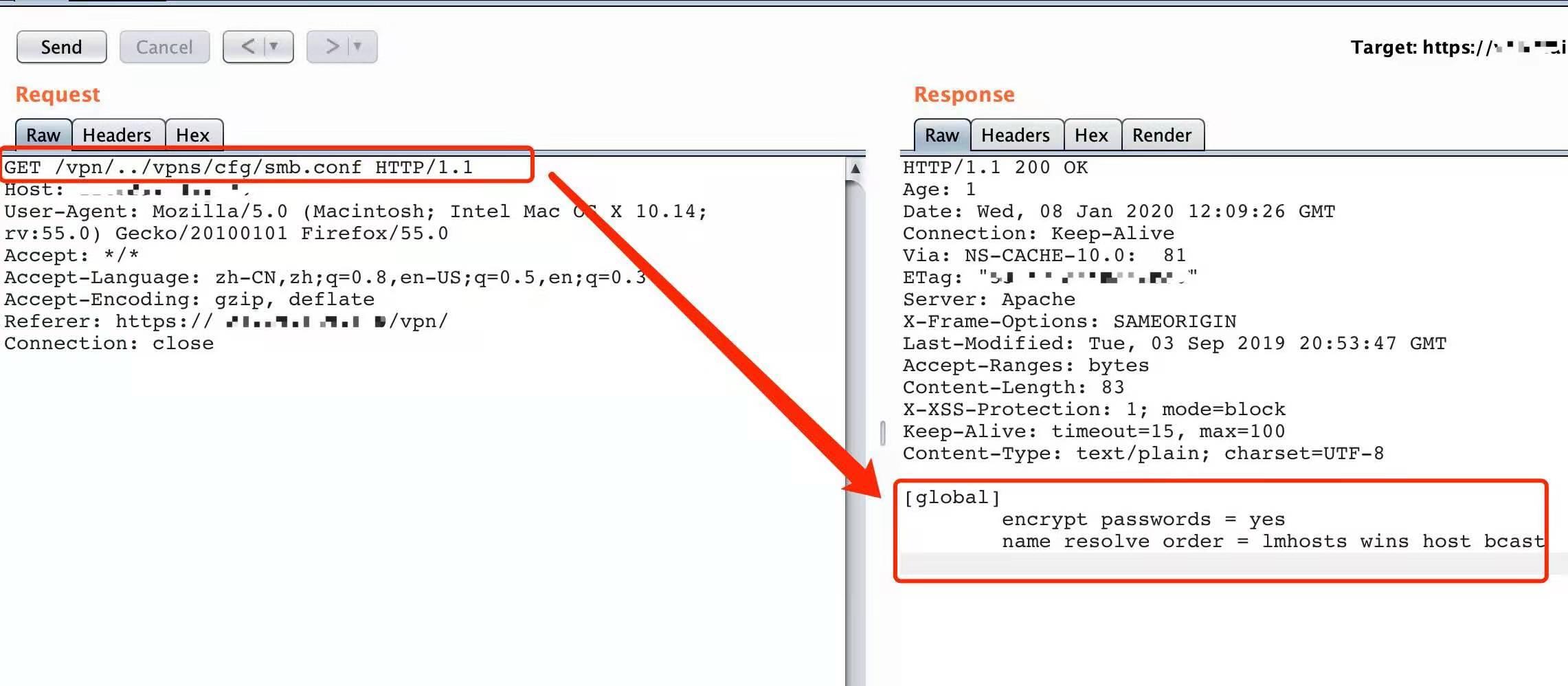
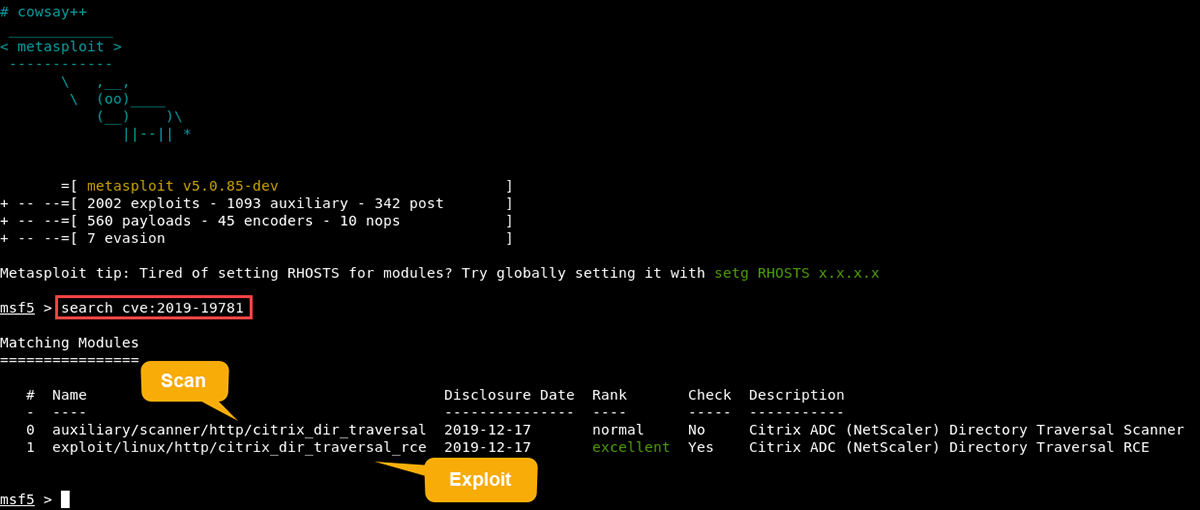
Exploits in the Wild for Citrix ADC and Citrix Gateway Directory Traversal Vulnerability CVE-2019-19781

How to Configure NetScaler Application Firewall Signatures Protection Based on Vulnerability Scan Result of QualysGuard

How to Configure NetScaler Application Firewall Signatures Protection Based on Vulnerability Scan Result of QualysGuard

CVE-2019-19781: Critical Vulnerability in Citrix ADC and Gateway Sees Active Exploitation While Patches are Still Not Available - Blog | Tenable®

CVE-2019-19781: Exploit Scripts for Remote Code Execution Vulnerability in Citrix ADC and Gateway Available - Blog | Tenable®