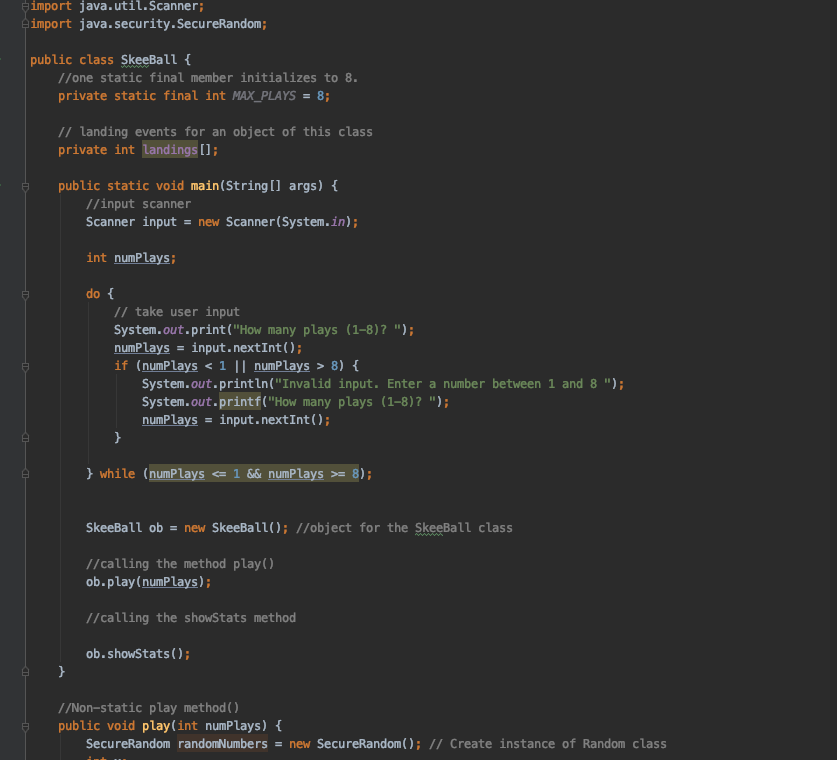
![PDF] Source Code Analysis to Remove Security Vulnerabilities in Java Socket Programs: A Case Study | Semantic Scholar PDF] Source Code Analysis to Remove Security Vulnerabilities in Java Socket Programs: A Case Study | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/27bfe8312bec6f30215a8eb92180a10a7672091f/6-Figure6-1.png)
PDF] Source Code Analysis to Remove Security Vulnerabilities in Java Socket Programs: A Case Study | Semantic Scholar
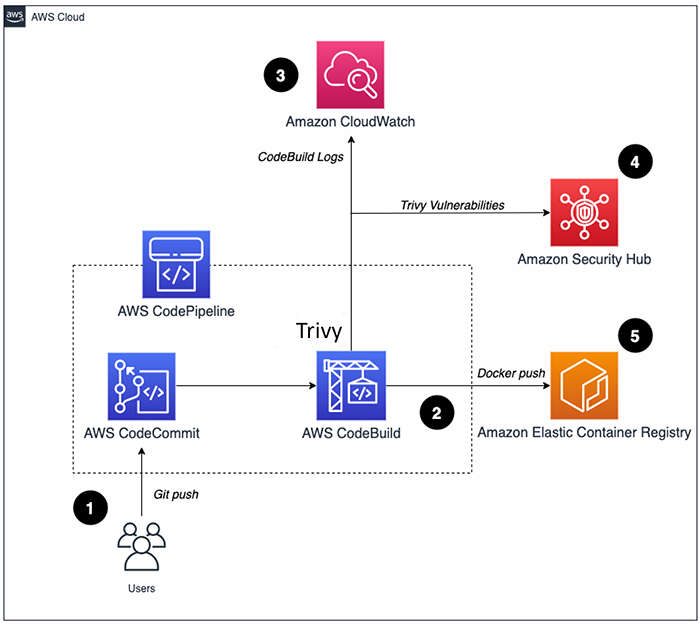
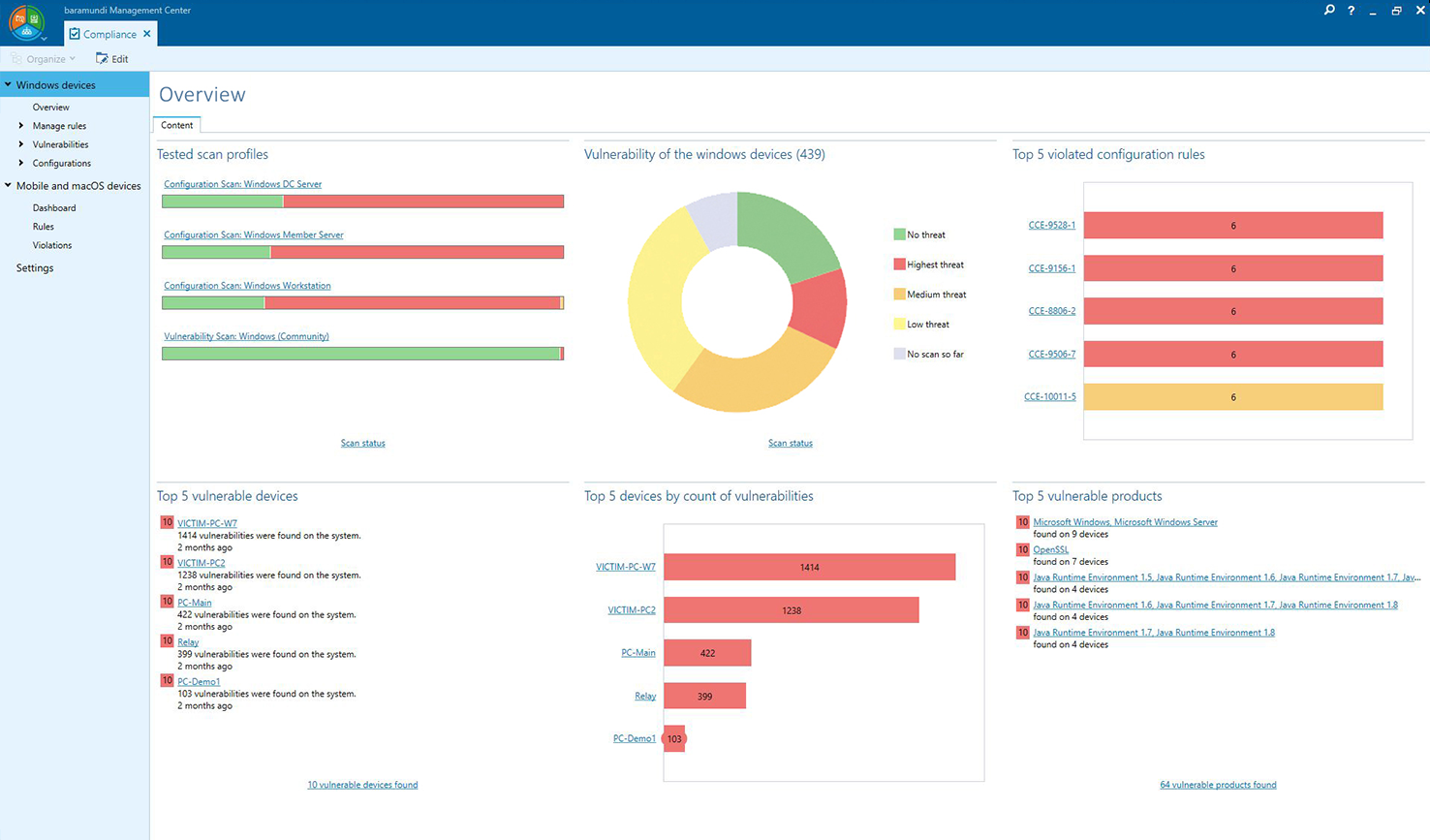
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

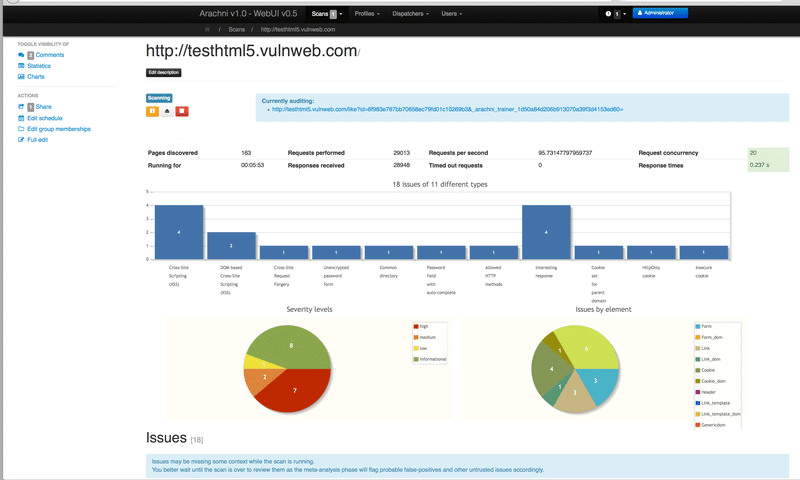
Java-Deserialization-Scanner - BurpSuite JAVA deserialization vulnerability scanning plug-in • Penetration Testing